CyberSecurity - The Introduction. Whether you sell online or not, it is very likely that you are using the internet to support your business - even if just through email, accessing the world wide web or publishing a basic website. Unfortunately, even at this minimal level, you are at risk. See: the short video explaining who might attack your organisation.
Indeed, a UK Government survey estimated that in 2018, 61% of large corporations and 31% of small businesses suffered a cyber breach. The average cost of a cyber-security breach is £22,700 for large businesses and £3,650 for small businesses. (The Association of British Insurers.) A further study by Hiscox showed a 15% rise in those figures in 2019. The results of a GOV.UK survey released in March 2020 confirms cyber security breaches are becoming more frequent. It found 46% of UK businesses and charities reported a cyber-attack during the year. Of those, 33% claimed they experienced a cyber breach in 2020 at least once a week – up from 22% in 2017.
Therefore, the risks to large, medium and small businesses are real and widespread. Here are 15 practical ways to keep your IT systems safe and secure:
- Password Protection: - Make sure you use strong passwords on smartphones, laptops, tablets, email accounts as well as any other devices or accounts where personal information is stored. Use strong passwords and multi-factor authentication. They must be difficult to guess. The National Cyber Security Centre (NCSC) recommends using three random words. Where possible, you should consider using multi-factor authentication. This requires at least two separate forms of identification before access is granted. For example, you use a password and a one-time code which is sent by text message.
- Data Backup: - You should back up your data regularly (at least daily). If you’re using an external storage device, keep it somewhere other than your main workplace – encrypt it, and lock it away if possible. Check your backup. You don’t want to find out the data has been corrupted when you need it most. Make sure your backup isn’t connected to your live data source so that any malicious activity doesn’t reach it. You should also respect any legal obligations covering the data you may hold and how you should hold this data.
- Hardware Failure: - This can mean not only that your access to the internet - and your email - is disrupted, but also that key information and programs that you rely on are deleted. By backing up data and programs and having spare smartphones and laptops, you can mitigate any hardware failure.
- Identities & eSignatures: - Confirm online identities and sign documents online; securely.
- Malware infecting your Smartphones and Computers: - These can not only cause your organisation all sorts of problems, but they can move on to infect your suppliers and customers. (Think how bad that would be for your reputation.) Install anti-virus and malware protection - and keep it up-to-date.
- Phishing Attacks: - Used to access sensitive information (access to bank accounts) and/or to install malware. You and your staff need to know how to spot suspicious emails. Look out for signs such as bad grammar, demands for you to act urgently and requests for payment. A phishing email could appear to come from a source you recognise. If you’re not sure, speak to the sender. NCSC provide useful training materials to help you and your staff recognise suspicious emails.
- Website Security: - If you use your website to exchange any sensitive information (e.g. orders, sales, credit card information and personal information), it is very important to install SSL/TLS Certificates to protect that information.
- Limit access to those that need it:- Different workers may need to use different types of information. Put access controls in place to make sure people can only see the information they need. For example, payroll or HR may need to see workers’ personal information, but your sales staff won’t. - If someone leaves your company, or if they’re absent for a long period of time, suspend their access to your systems.
- Be aware of your surroundings:- If you’re on a train or in a shared workspace, other people may be able to see your screen. A privacy screen might help you.
- Protect your device when it's unattended:- Lock your screen when you’re temporarily away from your desk to prevent someone else from accessing your computer or stealing your laptop. If you do need to leave your device for longer, put it in a secure place, out of sight. Consider what the consequences would be if your smartphones or computers were lost or stolen.
- Make sure your wi-fi connection is secure:- Using public Wi-Fi, or an insecure connection, could put personal data at risk. You should make sure you always use a secure connection when connecting to the internet. If you’re using a public network, consider using a secure Virtual Private Network (VPN).
- Take care when sharing your screen:- Sharing your screen in a virtual meeting may show your device to others exactly as you see it, including any open tabs or documents. Before sharing your screen, you should close anything you don’t need and make sure your notifications and pop-up alerts are switched off.
- Don't keep data for longer than you need it:- Getting rid of data you no longer need will free up storage space. This also means you have less personal information at risk if you suffer a cyber-attack or personal data breach.
- Dispose of old IT equipment and records securely:- You must make sure no personal data is left on computers, laptops, smartphones or any other devices, before you dispose of them. You could consider using deletion software, or hire a specialist to wipe the data.
- Insurance: - Finally, you may consider taking out insurance, should you suffer loss, notwithstanding the protection you have put into place. See whether Cyber Insurance is something you should consider to provide extra protection.
For a checklist of actions that you should consider\undertake see: The National Cyber Security Centre's (NCSC) Small Business Guide Actions.
You may also find it helpful to check out the NCSC's Small Business Guide: Cyber Security.
If you are dealing in any way online, it is very likely that you should be registered with the Information Commissioner's Office.
Why not carry out a quick online self-assessment to receive your CyberSecurity Guidance and Action Plan from IASME? (IASME is committed to helping businesses improve their cyber security, risk management and good governance through an effective and accessible range of certifications.)
See: Advanced CyberSecurity if you would like to consider advanced issues such as:
- Advanced Malware Protection.
- Artificial Intelligence Protection.
- Data Protection.
- Legal Considerations.
Finally, you should discuss CyberSecurity with your in-house IT team as well as your internet and website service providers. If you do not have a dedicated internal team to manage your CyberSecurity, we suggest that you read the National Cyber Security Centre's definition of Cyber Security.
If you feel that you would like advice from an independent consultant, then it is suggested that you see if the BSI's Cyber Security and Information Resilience Consultancy Service could help you.
Cyber Insurance covers the losses relating to damage to, or loss of information from, IT systems and networks.
If you feel that insurance cover is appropriate for your organisation, then you may consider the services provided by Hiscox Cyber insurance policies. You can review a non-binding quote in just 5 minutes. (For organisations that subscribe to one of CyberSmart's Pricing Plans, these will include a £25,000 insurance policy; terms apply.)
Any business, contractor or freelancer using the internet as part of their work could fall prey to cyber crime or face a data breach which insurance might help to resolve.
This means enterprises of all shapes and sizes could stand to benefit from cyber insurance. Nonetheless, certain professions may have a greater need than others.
- If your business operates primarily online or you handle large amounts of information, then cyber cover could play an important role in risk management.
- A marketing agency which experiences accidental data loss may face a privacy complaint leading to steep legal fees, for instance.
- Meanwhile, an IT consultant who relies on multiple software packages could lose income if these are locked by ransomware.
- Management consultants and accountants could require reputational support if a cyber-attack impacts their public image, while insurance brokers may incur additional expenses as they race to recover a compromised system – all kinds of professions can benefit from having the right cyber cover in place.
Data Protection: - You must make sure that you comply with relevant recommendations and regulations. In particular, you must conform to The General Data Protection Regulation 2016/679 (GDPR).
The Information Commissioner's Office (ICO) is the UK’s independent authority set up to uphold information rights in the public interest, promoting openness by public bodies and data privacy for individuals.
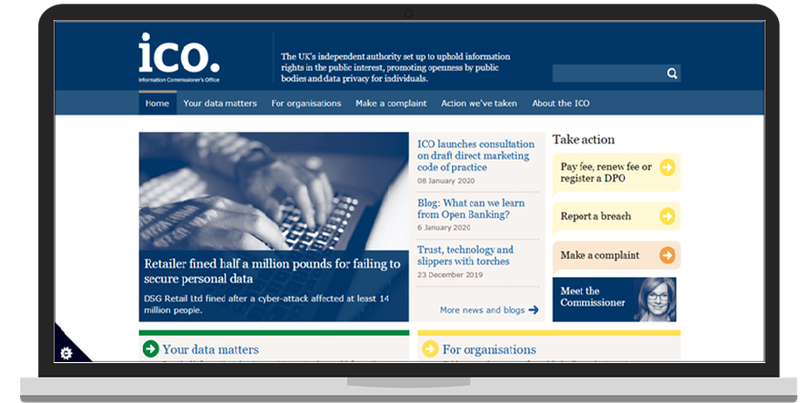
The ICO has published its data sharing code of practice, which provides clear guidance for organisations and businesses on how to share data lawfully. They have also produced new tools, such as a data sharing checklist and templates, to help you further.
The Data Protection (Charges and Information) Regulations 2018 requires every organisation or sole trader who processes personal information to pay a data protection fee to the ICO, unless they are exempt.
As at 1st January, 2020 there are three different tiers of fee and controllers are expected to pay between £40 and £2,900. The fees are set by Parliament to reflect what it believes is appropriate based on the risks posed by the processing of personal data by controllers.
The tier you fall into depends on:
- how many members of staff you have;
- your annual turnover;
- whether you are a public authority;
- whether you are a charity; or
- whether you are a small occupational pension scheme.
Not all controllers must pay a fee. Many can rely on an exemption.
Tier 1 – Micro Organisations
You have a maximum turnover of £632,000 for your financial year or no more than 10 members of staff. The fee for tier 1 is £40.
Tier 2 – Small and Medium Organisations
You have a maximum turnover of £36 million for your financial year or no more than 250 members of staff. The fee for tier 2 is £60.
Tier 3 – Large Organisations
If you do not meet the criteria for tier 1 or tier 2, you have to pay the tier 3 fee of £2,900. The ICO regards all controllers as eligible to pay a fee in tier 3 unless and until they tell the ICO otherwise.
Also see:
LawBite's 7 minute video "How to comply with GDPR rules".
CyberSmart's GDPR White Paper.
Hardware Failure can happen at any time putting your data and software at risk of loss. It is therefore very important to have a back-up system in place. Detailed UK Government advice on backing up your data can be found on the National Security Council's website.
The key points to consider when back-up your data are:
- Identify what data and programs you need to back-up.
- Keep your back-up separate from your computer.
- Consider using the cloud (e.g. Google Drive, Dropbox, Microsoft One Drive, etc.)
- Read the National Security Council's cloud security guidance.
- Make backing-up part of your business day (it can be easily automated).
Identity Fraud is one of the major risks when contracting online. There are steps you can take to reduce risk by checking the identity of the company and individual you are dealing with. Once you are sure of your partner's identity. You can also sign legally binding contracts via the internet.
There are 4 steps you should take here:
- Have you checked that the company is registered with the relevant Official Company Registration Office?
- Is the person you are dealing with authorised to negotiate\contract with you i.e. a director?
- Is the person you are dealing with actually that person?
- Have the documents you exchanged been legally signed by your counterparty?
Whether in the digital or physical world, you should carry out the same level of due diligence regarding both sets of identity.
Identity
We have suggested using First Report with regard to credit standing – but you can start with:
- In the UK, (free) searches at Companies House provide the details of UK companies
- The equivalent of Companies House for companies based in other countries. These are listed under “Company Register” in the relevant Country Commercial Contacts Profile.
Once you have confirmed the details of the company – and possibly also checked their entry in Kompass for further details – you can cross-check the identity of the person with whom you are dealing (are they a director)? (listed on the website?). Can they be reached via the company’s switchboard? Do they have a company email address?
eSignatures
eSignatures are now recognised under English Law. In fact, from a number of points of view, they are preferable to signatures written by hand. This greatly facilitates B2B eCommerce allowing for the electronic exchange of signed commercial documents.
LawBite's Document Management Platform provides not only a legal library, and a system for the management of electronic documents but also the facility to e-sign documents. Print or e-sign - You have the option to download, print or send your documents digitally to use e-signing.
See the video: Checking, e-Signing and filing.
N.B. An eSignature is not simply a scanned image of a handwritten signature pasted into a document.
Electronic signatures provide three quantifiable benefits:
- Speed of Signing
Electronic agreements can be signed at a fraction of the time of paper-based agreements, especially when signatories are not in the same physical location.
- Sustainability
Signing electronically also results in reduced paper usage and the environmental impact of physically transporting agreements between locations.
- Greater Security
With proper identity verification methods and audited IT infrastructure, an electronic signature is much more secure than paper-based signings.
Considerations for Choosing your eSignature Solution
- How many electronic signatures do you expect to do?
- What are your use cases? B2C, B2B, C2C, B2E (employee)?
- How sure do you need to be on the identity of those signing? Under the EU eIDAS regulation, there are three levels of assurance as to the degree of confidence in the claimed identity of a signatory. These levels are: Low, Substantial, and High. The UK equivalent can be found at the ICO site.
- Do you have any business system workflow you need to integrate with?
- How future-proof do you need your signed agreements to be?
- Can you trust your provider?
- Can you trust the timing of the signatures? If needed, use a Qualified Trust Service Provider, who can guarantee the time, in the same way, it guarantees the identity of the signer. Technically, this is called a time-stamp, which is added to the document in a similar way as a signature, and the QTSP is the entity that guarantees that the time-stamp is correct and can be trusted.
- Do you envisage signing multiple documents with one signature?
- Do you need multiple people to sign single documents?
- Do you want to forward agreements for signing?
How should your eSignatures be delivered?
- Email Delivery
Many signing solutions rely on email-based delivery of an agreement without requiring any additional form of identity verification.
- Scribble on a Screen
This, in many cases, is the typical replacement for paper-based signatures and is familiar for the users. Unfortunately, this gives no assurance of the signer’s identity.
- SMS OTP
SMS OTP is the process of sending a random code to a mobile number, and this code is input to show that it has been received. This proves that the user signing has access to the device, but does not provide verified identification.
- Signing with a third-party Electronic ID
Some countries, particularly in the Nordics and Benelux regions, have access to third-party electronic identities (such as BankID), as provided by their governments or banks. These eIDs can be used to sign electronic agreements.
- Signing with Identity Documents
Some signing solutions leverage ID document scanning (such as passport or driver’s license) or NFC reading of the document as a way to verify the signer’s identity.
Document Security & Future Proofing Agreements
When generating digital signatures, digital certificates are involved. A digital certificate has an expiry time, after which it is no longer valid. It may also be revoked at any time, and the certificate authority maintains lists of these revoked certificates.
Digital signatures are based on mathematical algorithms, which can be attacked by advances in mathematics, software, and hardware. The algorithms used for digital signatures 10 years ago are no longer secure, and it is simple to forge a document that looks like it was signed 10 years ago.
The above challenges are addressed by adding long-term-validation information into the document. This is done by a Qualified Trust Service Provider, which collects all the evidence and embeds this into the signed document. (See tScheme Members for UK TSPs or The EU Commission site for EU TSPs.)
Keep Your Mobile Devices Safe. It is of course important to keep your mobile devices safe. However, there is always the risk that they will be lost or stolen; in which case you will need procedures in place to track them and keep safe the data stored on them. Detailed UK Government advice on keeping your mobile safe can be found on the National Security Council's website.
The key points to consider when implementing mobile device protection policy are:
- Switch on password protection.
- Make sure lost or stolen devices can be tracked, locked or wiped.
- Keep your advice up to date.
- Keep your apps up to date.
- Don't connect to unknown WiFi Hotspots.
Malware puts everyone at risk. There are different types of malware - none of them are good all of them are being widely circulated. No matter how small your business you must have malware protection systems in place. Detailed UK Government advice on protection from malware can be found on the National Security Council's website.
The good news is that protection need not be expensive (indeed many services are free of charge - however, these will necessarily offer lower levels of protection than more expensive services).
The key points to consider when implementing your anti-malware protection are:
- Install and turn on your antivirus software. (Service providers are listed here.)
- Prevent staff from downloading dodgy apps.
- Keep all your IT equipment up to date (patching).
- Control how USB drives (and memory cards) can be used
- Switch on your firewall.
Password Protection is a key method of protecting access to your organisation's sensitive commercial data. (Detailed UK Government advice on keeping your data safe can be found on the National Security Council's website.) However, when using passwords you should consider the following:
- Make sure you switch on password protection.
- Use two-factor authentication for important accounts.
- Avoid using predictable passwords.
- Help your staff cope with password overload.
- Change all default password.
- When an employee leaves your employment, change all passwords that they had previously used.
- Have a secure password back-up system - make sure that you cannot be locked out of information by the absence of an employee.
Phishing attacks occur when an attacker sends a fraudulent (e.g., spoofed, fake, or otherwise deceptive) message designed to trick a human victim into revealing sensitive information to the attacker or to deploy malicious software on the victim's infrastructure. These messages can be sent by any communication channel e.g. telephone, email, text, whatsapp, social media etc.). Detailed UK Government advice on keeping your data safe can be found on the National Security Council's website.
It should be emphasised that phishing attacks are becoming ever more sophisticated. However, the following should help you identify the most common phishing attacks:
- Configure accounts to reduce the impact of successful attacks.
- Think about how you operate.
- Check for the obvious signs of phishing.
- Report all attacks.
- Check your digital footprint.
Reporting CyberCrime helps everyone. If you suffer a CyberCrime or thwart an attempt at CyberCrime, it helps everybody if you report this to the competent authorities. In the UK, these are:
- Action Fraud
Provides a single reporting system for people to report financially motivated cyber-crime. - Centres of Excellence for Cyber Security Research
A network within UK universities to help provide reliable and up to date research and academic prowess. - Computer Emergency Response Team (CERT)
Launched to improve national co-ordination of cyber incidents. - Cyber Incident Response
Based in GCHQ, this scheme helps organisations recover from a cyber security attack. - Cyber Security Information Sharing Partnership (CiSP)
Allows Government and industry to exchange information on cyber threats in real time. - National Cyber Security Centre (NCSC)
Provides a unified source of advice, guidance, and support on cyber security, including the management of cyber security incidents. - National Cyber Crime Unit (NCCU)
A dedicated Cyber-crime unit that sits within the National Crime Agency.
The Information Commissioner's Office (ICO) is responsible for enforcing the rules on spam texts. Incidents where data is compromised or stolen could breach GDPR, so these must be reported to the ICO within 72 hours to minimise possible penalties.
If you receive a suspicious email, text message, telephone call that claims to be from Royal Mail or discover a Royal Mail branded website which you think is fraudulent, please report it.
Ofcom also provide advice on how to avoid unwanted calls and messages as well as a guide to reporting scam texts or mobile calls.
Website Security. Websites secured by a TLS/SSL certificate will display HTTPS and the small padlock icon in the browser address bar. TLS/SSL certificates are used to protect both the end users’ information while it’s in transfer, and to authenticate the website’s organisation identity to ensure users are interacting with legitimate website owners - and the address begins https:// rather than just http:// where the “s” stands for secure.
Invisible to the end-user, a process called the “TLS/SSL handshake” creates a protected connection between your web server and web browser nearly instantaneously every time you visit a website.
SSL/TLS Certificates need to be issued from a trusted Certificate Authority – you can find a list of SSL/TLS Certificate Service Providers on The ExportersAlmanac – Secure Certificate Providers.
See the NCSC article “Using TLS to protect data” and GlobalSign’s “SSL vs TLS – What’s the Difference?”